Blockchain
Security Testing
iSpyCyber provides expert-led blockchain penetration testing to secure smart contracts, dApps, and blockchain networks from advanced cyber threats. Our compliance-ready audits align with OWASP, ISO 27001, and GDPR, identifying vulnerabilities and logic flaws early. Protect your blockchain ecosystem, ensure compliance, and build user trust with iSpyCyber’s trusted blockchain security solutions.
BLOCKCHAIN Security Services
Smart Contract & dApp Security Assessment
- Comprehensive security analysis of smart contracts, dApps, and blockchain logic
- Manual review + automated SAST/DAST + AI-based vulnerability detection
- Identifies re-entrancy, overflow/underflow, logic flaws, access control issues, and privilege misuse
- Testing aligned with OWASP, SANS, PTES, Smart Contract Security Best Practices
- Compliance-ready reporting for SOC 2, ISO 27001, HIPAA, GDPR
infrastructure & Node Security Assessment
- Security assessment of blockchain nodes, validators, full nodes, and network infrastructure
- Identifies misconfigurations, consensus manipulation risks, DDoS exposure, RPC vulnerabilities, and key management weaknesses
- Evaluation includes firewall rules, network hardening, encryption, and identity controls
- Follows OWASP, SANS, PTES, NIST security frameworks
- Provides risk-based remediation guidance for secure and stable node operations
Wallet, API & Integration Security Assessment
- End-to-end security review of crypto wallets, APIs, payment gateways, and blockchain integrations
- Detects insecure key storage, weak encryption, API abuse risks, injection flaws, and transaction tampering
- Manual pentest combined with automation and AI-driven threat modeling
- Adheres to OWASP API Security Top 10, Wallet Security Best Practices, and Blockchain Integration Guidelines
- Includes compliance-supportive documentation for audits (SOC 2, ISO 27001, HIPAA)
GRC and Continuous Security Assessment
- Governance, Risk & Compliance evaluation for blockchain-enabled environments
- Continuous monitoring of risks, vulnerabilities, configurations, and security posture
- Framework-based assessment using NIST CSF, ISO 27001, SOC 2, GDPR, HIPAA
- Includes policy review, security controls mapping, process maturity assessment, and ongoing advisory
- Helps maintain continuous compliance, audit readiness, and operational resilience
Enterprise
- Dedicated Customer Success manager for your organization
- Custom SLA/Contract as per requirements
- Multiple payment option
- 2 Re-scans by experts to verify fixes period for 1 Year*
- Unlimited retest of web application
Key Benefits
It’s an important practice that gives organizations visibility into real-world threats to your security. As part of a routine security check, penetration tests allow you to find the gaps in your security before a hacker does by exploiting vulnerabilities and providing steps for remediation.
Our VAPT Sevices
Explore more resources with iSpyCyber for cutting-edge cybersecurity blogs, insights, tools, and others to stay ahead of threats.
Web Application
VAPT
Secure your websites with
comprehensive vulnerability testing to
identify risks, prevent data breaches, and
ensure robust application protection.
Mobile Application
VAPT
Protect Android and iOS apps against
evolving cyber threats by identifying
vulnerabilities, securing user data, and
maintaining compliance standards.
Network / Infra. VAPT
Strengthen internal and external
networks by identifying vulnerabilities in
servers, routers, and firewalls through
advanced penetration testing.
Thick client
Application VAPT
Assess desktop applications for
vulnerabilities in authentication, logic,
and data handling to strengthen security
and prevent exploitation.
API VAPT
Safeguard APIs from unauthorized
access and data breaches through
advanced testing that ensures integrity,
authentication, and endpoint protection.
SAP Application
VAPT
Protect critical SAP systems from
misconfigurations, privilege escalation,
and data breaches through deep security
assessments and remediation.
Blockchain
Application VAPT
Enhance blockchain resilience by
auditing smart contracts, consensus
mechanisms, and cryptography to
eliminate potential financial or
operational risks.
IoT VAPT
(Internet of Things)
Defend connected devices by testing
firmware, communication protocols, and
configurations to ensure secure IoT
environments and data protection.
OT VAPT
(Operational Tech.)
Safeguard industrial control systems by
identifying vulnerabilities in SCADA, PLC,
and ICS environments to prevent
operational disruptions.
Compliance Commitment as Per Your Requirement










blockchain security Resources
It’s an important practice that gives organizations visibility into real-world threats to your security. As part of a routine security check, penetration tests allow you to find the gaps in your security before a hacker does by exploiting vulnerabilities and providing steps for remediation.
Why iSpyCyber ?
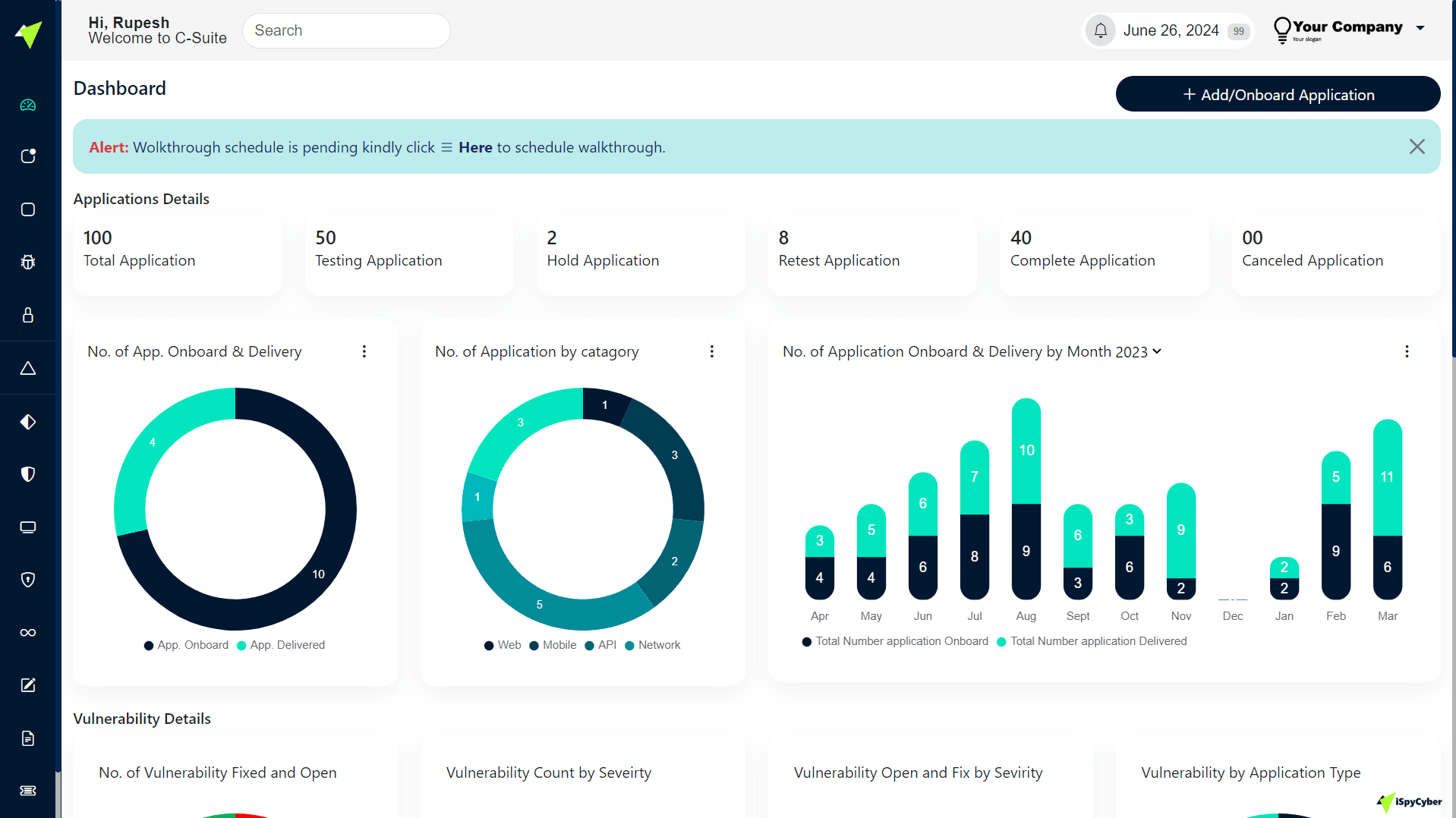
100%
Certified Professional
0%
Outsourcing
100%
Dashboard Reporting
100%
Data Sovereignty Assured
We prioritize the well-being of our clients and value their privacy and security above all else. Our dedicated team, equipped with extensive training and a thorough testing protocol, surpasses mere compliance checkboxes to fully grasp each client's distinct penetration testing requirements. Through a collaborative process, we ensure that our clients comprehend our detailed reports and assessments. Moreover, we offer guidance in delineating the subsequent measures to fortify their security infrastructure through a comprehensive cybersecurity strategy.
9100+
Total No. Vulnerabilities
15+
Countries Served
150+
Assessment Completed
30+
Trusted Clients
We prioritize the well-being of our clients and value their privacy and security above all else. Our dedicated team, equipped with extensive training and a thorough testing protocol, surpasses mere compliance checkboxes to fully grasp each client's distinct penetration testing requirements. Through a collaborative process, we ensure that our clients comprehend our detailed reports and assessments. Moreover, we offer guidance in delineating the subsequent measures to fortify their security infrastructure through a comprehensive cybersecurity strategy.
Discover more Resources
Explore more resources with iSpyCyber for cutting-edge cybersecurity blogs, insights, tools, and others to stay ahead of threats.
FAQ
Vulnerability Assessment and Penetration Testing (VAPT) is a comprehensive security process that identifies, analyzes, and mitigates vulnerabilities within your IT systems, networks, and applications. It helps organizations like yours prevent data breaches, protect critical assets, and comply with cybersecurity standards. At iSpyCyber, our expert team ensures your digital environment remains secure and resilient against evolving cyber threats.
iSpyCyber follows a systematic and industry-recognized VAPT methodology that includes information gathering, vulnerability scanning, manual verification, exploitation testing, risk evaluation, and reporting with remediation guidance. We combine automated tools and manual testing to uncover real-world vulnerabilities and simulate hacker-like attacks — ensuring your organization is truly protected.
Every system connected to the internet or internal network should undergo VAPT. This includes web applications, mobile apps, APIs, cloud infrastructure, IoT devices, network systems, and critical databases. iSpyCyber customizes VAPT services to fit your business environment — whether you’re a startup, enterprise, or government organization — ensuring full security coverage.
It’s recommended to perform VAPT at least once a year, or whenever there are significant changes such as new deployments, software updates, or infrastructure modifications. Regular VAPT testing by iSpyCyber ensures that newly introduced vulnerabilities are quickly identified and mitigated, maintaining ongoing compliance and security readiness.
After the assessment, iSpyCyber provides a detailed VAPT report that includes:
Executive summary for management review
Comprehensive list of identified vulnerabilities
Risk rating (Critical, High, Medium, Low)
Technical details with screenshots and evidence
Remediation recommendations for each finding
These insights help your security and development teams take immediate, effective action to strengthen defenses.
At iSpyCyber, we strictly adhere to data confidentiality and ethical testing standards. All assessments are conducted under mutual NDAs (Non-Disclosure Agreements) and authorized testing scopes. We never disrupt business operations or access client data without consent — ensuring a safe, controlled, and compliant VAPT process that meets global security benchmarks like ISO 27001, NIST, and OWASP.